Another data leak, this time involving, let’s see, 1.2 billion people. This was found by security researchers in an unsecured ElasticSearch server – the server is now down. According to analysis, the data most likely comes from data enrichment companies.
A total count of unique people across all data sets reached more than 1.2 billion people, making this one of the largest data leaks from a single source organization in history. The leaked data contained names, email addresses, phone numbers, LinkedIN and Facebook profile information.
…
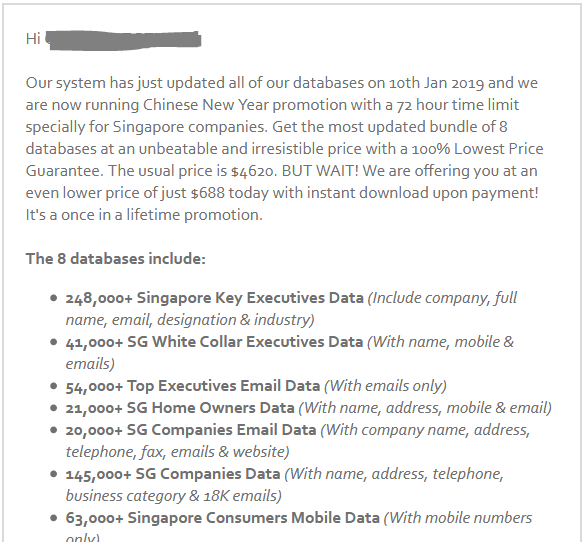
For a very low price, data enrichment companies allow you to take a single piece of information on a person (such as a name or email address), and expand (or enrich) that user profile to include hundreds of additional new data points of information.
Source: 1.2 billion people exposed in data leak includes personal info, LinkedIN, Facebook