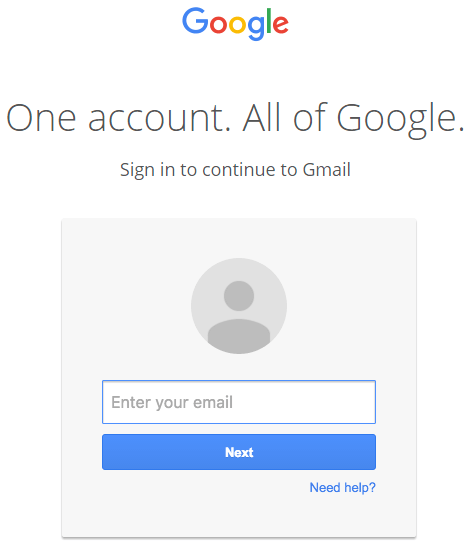
Phishing attacks are getting more creative, relying on moments of weakness in human perception. The tried-and-tested phishing method normally includes the domain name of the target site as part of the URL (eg. paypal.com-privacyprotection.com) and hope that the user doesn’t notice the actual domain (com-privacyprotection.com). This method takes it to another level ‘cos you will see the actual URL of the target site.
A new phishing technique that affects GMail and other services and how to protect yourself.
Source: Wide Impact: Highly Effective Gmail Phishing Technique Being Exploited