NSA develops cyberweapons. Cyberweapons gets leaked. Everyone who’s unprotected gets compromised.
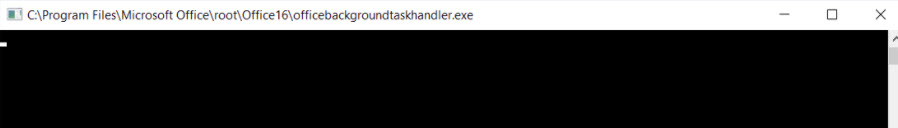
Thousands of Microsoft Windows machines worldwide are infected with an NSA-developed backdoor that hackers installed by reusing leaked executable code from an outdated hacking toolkit belonging to the spy agency, multiple security researchers tell CyberScoop. The mysterious Shadow Brokers group published a package of internal NSA documents last week, containing among other things the computer code for a series of exploits, implants and other hacking tools. In the days since the leak first became public, hackers have mulled over the trove and begun reverse-engineering and recycling some of the capabilities, CyberScoop previously reported. One of these hacking tools, a backdoor implant codenamed DOUBLEPULSAR — which is used to run malicious code on an already compromised box — has already been installed on 30,000 to 50,000 hosts, according to Phobos Group founder Dan Tentler. Other researchers have also engineered different detection scripts to quickly scan the internet for infected computers. John Matherly, […]
Source: That was fast: Thousands of computers now compromised with leaked NSA tools, researchers say – Cyberscoop