“Why stop at 4?”
Nokia’s next flagship Android phone features five cameras, a 5.99-inch PureDisplay, more.
Source: Nokia’s Next Android Flagship Features Five Cameras – Thurrott.com
“Why stop at 4?”
Nokia’s next flagship Android phone features five cameras, a 5.99-inch PureDisplay, more.
Source: Nokia’s Next Android Flagship Features Five Cameras – Thurrott.com
In a move that has sent shock waves through the cybersecurity and software community, Australia passes new law that could potentially devastate its software industry, by compelling tech companies to help law enforcement break into user’s encrypted data.
Both countries now claim the right to secretly compel tech companies and individual technologists, including network administrators, sysadmins, and open source developers – to re-engineer software and hardware under their control, so that it can be used to spy on their users. Engineers can be penalized for refusing to comply with fines and prison; in Australia, even counseling a technologist to oppose these orders is a crime.
Source: In the New Fight for Online Privacy and Security, Australia Falls:
A novel way of scamming. Make your phone number appear in Google Maps by claiming it. People who clicks on the result of Google Maps gets directed to you. Profit!
When you see any information listed on a website, your first reaction isn’t to immediately question whether or not that information is accurate. It is to blindly trust the technology that has helped you unfailingly countless times in the past. That is precisely why this scam is so potent.
Source: New form of Google banking scam
Great story based on a true hacking attempt.
Except for the last bit which was dramatized, the author gave a fairly good first-person account of an internal pentesting being carried out. It involves everything from impersonation, social engineering, physical theft, wits and a good amount of luck.
“Good afternoon, Pam. I’m Josh from IT. We’re about to migrate your Citrix instance to a new server. I’m going to send you a 6 digit number. I’ll need you to read that off to me. As a reminder, IT will never ask for your password.”
I already had her password.
She gave a hesitant, “Okay…”
I clicked on the “Click for MFA token” button and stated, “Alright, I’ve sent you the number. You should get a text. Please read it to me.”
She said, “Umm, alright. Got it. It’s 9-0-5-2-1-2.”
Source: A thread written by @TinkerSec
Woops. YouTube is down at the moment.
It’s interesting that Google chooses to display an encrypted message (presumably containing details of the error) on the client browser. This is certainly a novel way for users to report the problem without exposing potentially sensitive details (eg. file paths) to them.
YouTube is down and reports are coming in worldwide about the service being unavailable.
Source: YouTube Down According to Reports Worldwide & Twitter Reacts
Update: Service is up after about 2 hours
Bloomberg’s big story on alleged China hacking through server hardware implants. If true, it would be an absolutely incredible feat, equivalent in terms of impressiveness to the Stuxnet worm.
The attack by Chinese spies reached almost 30 U.S. companies by compromising America’s technology supply chain.
Source: The Big Hack: How China Used a Tiny Chip to Infiltrate U.S. Companies – Bloomberg
At the moment, Bloomberg seems to double-down on its story with the following statement:
“Bloomberg Businessweek’s investigation is the result of more than a year of reporting, during which we conducted more than 100 interviews,” a spokesperson told BuzzFeed News in response to a series of questions. “Seventeen individual sources, including government officials and insiders at the companies, confirmed the manipulation of hardware and other elements of the attacks. We also published three companies’ full statements, as well as a statement from China’s Ministry of Foreign Affairs. We stand by our story and are confident in our reporting and sources.”
It’ll be interesting to see who’s telling the truth as the story develops. Meanwhile, governments and companies around the world should be in panic mode, as they try to figure out if they are using Supermicro servers, and if so, whether they are affected by the so-called hacking.
(2018-Oct-04) Apple and Amazon both issued strong denials to the claims of the article.
(2018-Oct-04) Separately, Apple and Amazon both issued even stronger statements on their website to set the record straight on the matter.
(2018-Oct-05) Buzzfeed’s coverage of the story also seem to indicate that even senior staff in Apple doesn’t know about the alleged hacks.
(2018-Oct-20) Apple CEO Tim Cook Is Calling For Bloomberg To Retract Its Chinese Spy Chip Story
(2018-Oct-23) Amazon cloud chief Jassy follows Apple in calling for retraction of Chinese spy chip story
For those who are wondering about the alleged soft filter on the iPhone XS, and other details about the new iPhone XS camera.
What’s this about a ‘soft filter’ on my selfies? It doesn’t exist.
The so-called unified QR code is finally out.
SGQR code is purportedly Singapore’s effort in “unifying” the fragmented e-payment market – what with DBS PayLah!, Singtel Dash, Grab Pay, LiquidPay, AliPay etc coming into the fray.
For consumers
Your current payment app probably works with SGQR already. All you need to do at the merchant checkout is:
• PICK and launch your preferred payment app
• SCAN the SGQR and check the merchant name
• PAY the correct amount
In other words, ideally a consumer can use his/her preferred payment app to make payment to a merchant through SGQR.
There are some upsides and some downsides. On the upside, consumer will only see one QR code per merchant. So it is less confusing compared to now where the payer have to carefully match the array of QR codes being shown to the right app.
On the downside, while the SGQR specification can enable multiple e-payment providers, merchants are unlikely to sign up with ALL of them (up to 27 payment schemes). So you can end up in a situation where you see a SGQR code but are unable to use your preferred payment app (say Grab Pay) to make payment. The payer have to look at the row of icons below the QR code to know which e-payment solution is accepted.
Very little technical information is publicly available about this SGQR code. After some research, I found on MAS website that it’s based on EMVCo QR code. EMVCo is made up of members from American Express, Discover, JCB, Mastercard, UnionPay, and Visa, and is the body that creates standards for secure payment.
Let’s try and see what the QR code contains. Fortunately the QR code in the article is clear enough to be decoded:
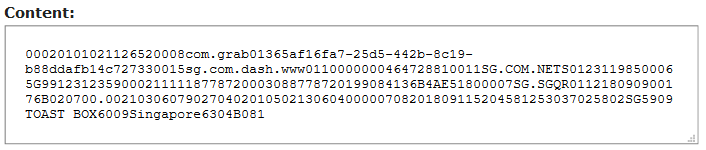
To parse the content of the QR code, one can refer to the EMVCo QR code specifications which is available on the EMVCo website.
After a bit of parsing,
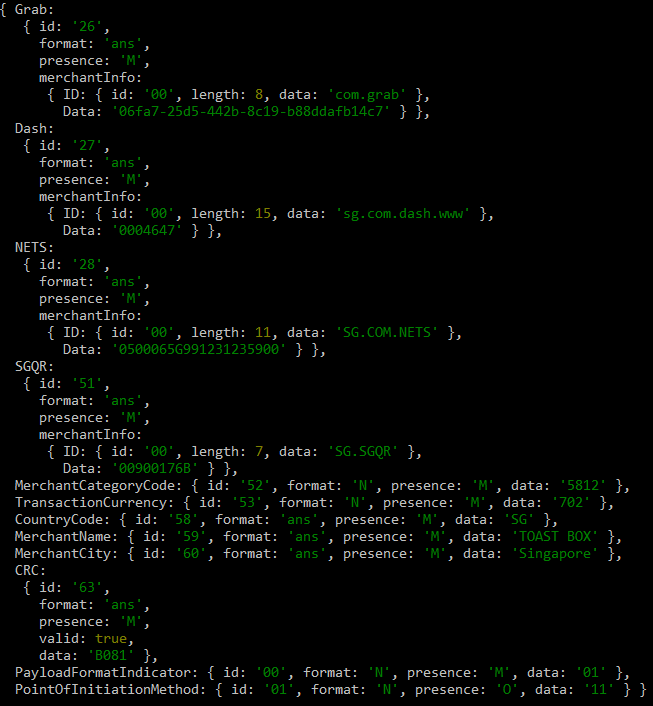
It’s clear that this QR code contains meta-data for only some payment providers.
We are still in the early days of SGQR. It remains to be seen how widely adopted businesses and consumers will take to this form of payment.
For now, the only thing it probably saves is real-estate for display QR codes.
Update (2018-09-21): Yeah! This article made it onto the front page of Hacker News! See the comments on HN here.
Remember this next time you’re on a Dreamliner.
Basically it says that all Boeing 787 Dreamliners have to be switched off every 248 days. If they are not reset then the generator control units GCUs will go into failsafe mode and the plane will lose all electrical power.
Source: Reboot Your Dreamliner Every 248 Days To Avoid Integer Overflow
We are in an age where the proliferation of sensors to collect data for analytics is becoming common-place. However there needs to be more caution in completely trusting the result of the data collected, eg. sensors can malfunction, there may be software errors, unprotected endpoints can be hacked etc.
The error resulted from a faulty sensor over the main entrance that was initially detected in the spring of last year, a museum representative said. At that time, an engineer was sent to repair the device, but the device later failed a routine accuracy test in July last year.