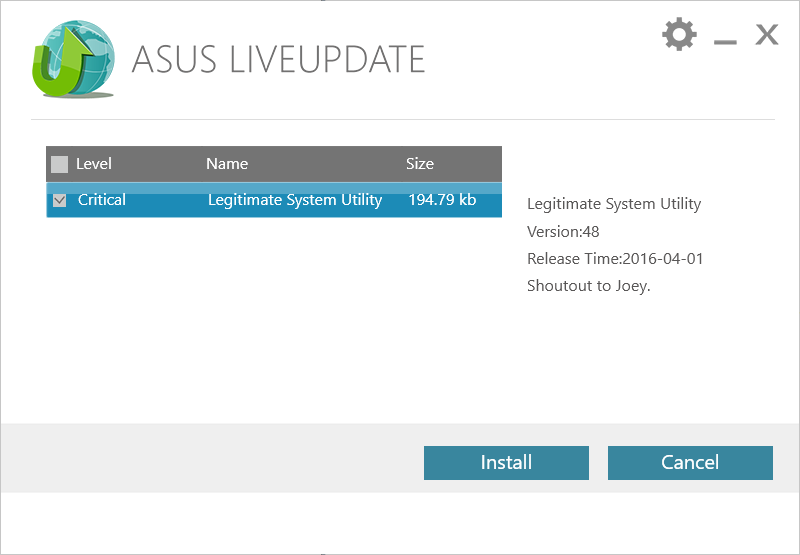
Your secrets should be safe as long as your machine is not connected to any network right? Think again. There have been extremely innovative ways of transmitting information from unplugged (or what is known as air-gapped) computers to other devices, including:
- using inaudible acoustic signals via built-in speakers
- using GPU as a FM transmitter
- wireless keyboard/mouse
- computer fan
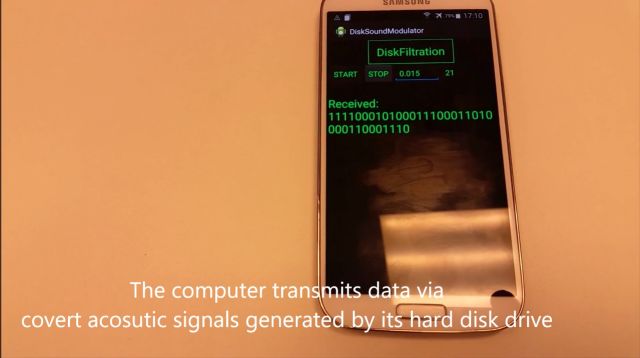
and now.. via the sound that a hard drive makes.
“DiskFiltration” siphons data even when computers are disconnected from the Internet.
Source: New air-gap jumper covertly transmits data in hard-drive sounds