An inside look into the workings of a cybercrime organization. For an organization that purportedly develops sophisticated malware to steal banking credentials, the lack of basic cyber hygiene led to much info being extracted about their dealings. The irony.
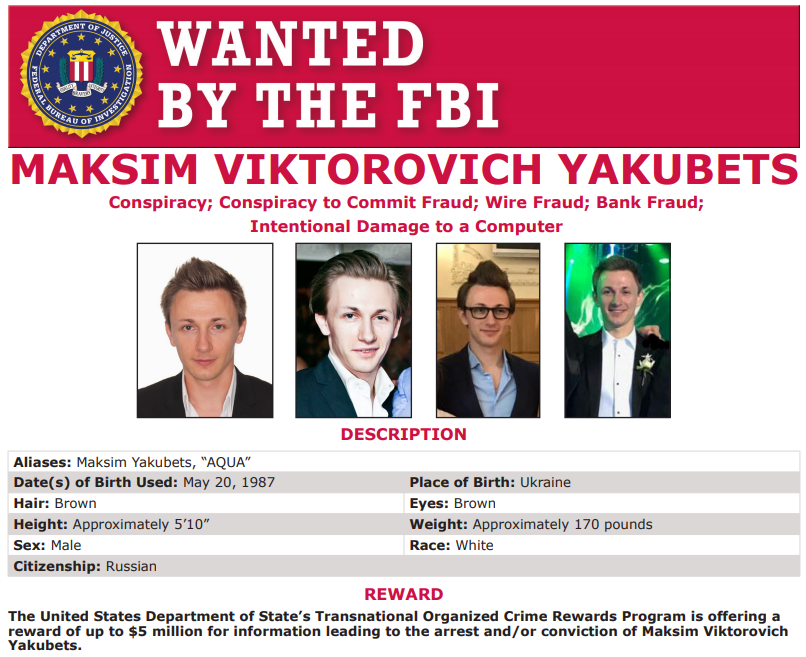
The $5 million reward is being offered for 32 year-old Maksim V. Yakubets, who the government says went by the nicknames “aqua,” and “aquamo,” among others. The feds allege Aqua led an elite cybercrime ring with at least 16 others who used advanced, custom-made strains of malware known as “JabberZeus” and “Bugat” (a.k.a. “Dridex“) to steal banking credentials from employees at hundreds of small- to mid-sized companies in the United States and Europe.
Source: Inside ‘Evil Corp,’ a $100M Cybercrime Menace — Krebs on Security