Internet vigilante to the rescue? Someone – or some group of people – decided the best way to save the Internet from the scourge of insecure IoT devices is to disable them permanently. I like how he/she/they describes his/her/their project.
I consider my project a form of “Internet Chemotherapy” I sometimes jokingly think of myself as The Doctor. Chemotherapy is a harsh treatment that nobody in their right mind would administer to a healthy patient, but the Internet was becoming seriously ill in Q3 and Q4/2016 and the moderate remedies were ineffective. The side effects of the treatment were harmful but the alternative (DDoS botnet sizes numbering in the millions) would have been worse. I can only hope hope that when the IoT relapse comes we’ll have better ways to deal with it. Besides getting the number of IoT DDoS bots to a manageable level my other key goal has been to raise awareness. The IoT problem is much worse than most people think, and I have some alarming stories to tell.
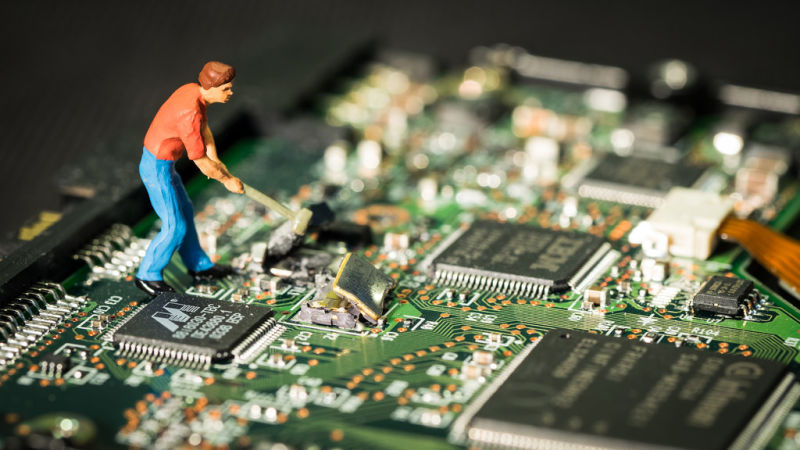
Source: This Hacker Is My New Hero